Unified Log Analytics
Every device, application, and service in your IT environment generates logs — timestamped records of what happened, when it happened, and what state the system was in. Individually, these logs are just data. Collectively, when unified and correlated, they become the single most powerful tool for understanding operational health, detecting security threats, and proving compliance.
The problem most IT organizations face isn't a lack of log data. It's the opposite: too many logs, from too many sources, in too many formats, scattered across too many tools. Engineers spend more time finding and parsing the right log than they spend actually diagnosing the issue. Security teams can't correlate events across systems fast enough to detect active threats. Compliance officers manually assemble reports from disconnected data stores.
Unified log analytics solves this by bringing every log stream into a single platform with real-time search, automated correlation, and actionable intelligence. Here's how it works and why it matters.
What Is Unified Log Analytics?
Unified log analytics is the practice of collecting, normalizing, storing, and analyzing log data from all sources across an IT environment through a single, centralized platform. Unlike traditional log management — which often involves separate tools for different log types — unified analytics treats every log as part of one interconnected data set.
A unified log analytics platform handles:
Collection — ingesting logs from servers, network devices, applications, cloud services, security tools, and custom sources
Normalization — converting diverse log formats into a consistent, searchable structure
Storage — retaining raw and processed log data for operational analysis, forensic investigation, and compliance requirements
Analysis — applying search, correlation, pattern detection, and machine learning to extract actionable insights
Visualization — presenting log data through real-time dashboards, alerts, and reports
Why Siloed Log Management Creates Operational Risk
Most IT environments don't start with siloed log management by design. It happens gradually — a monitoring tool for network devices, a separate SIEM for security logs, application-specific logging in each dev team's preferred format, and cloud-native logging services that don't integrate with on-premises tools.
The consequences are predictable and costly:
Slow root-cause analysis — when an incident spans multiple infrastructure layers, engineers must manually search across separate tools to piece together the timeline
Security blind spots — attackers who move laterally across systems exploit the gaps between disconnected log repositories
Compliance audit failures — auditors expect comprehensive, correlated log evidence; assembling it from multiple sources under audit pressure is error-prone and time-consuming
Alert fatigue — without correlation, every anomaly generates an independent alert, burying real issues in noise
Unified log analytics eliminates these risks by making every log event part of a single, queryable, correlated dataset.
Core Capabilities of a Unified Log Analytics Platform
Format-Agnostic Log Ingestion
Enterprise environments generate logs in dozens of formats — syslog, JSON, CSV, Windows Event Log, proprietary application formats, cloud provider-specific schemas, and more. A unified platform must ingest all of them without requiring source-side changes.
Motadata's AI-native log analytics engine handles any log format from any source. The platform normalizes incoming data automatically, so teams don't waste time writing custom parsers or reformatting logs to fit a rigid schema. If a source generates a log, Motadata can process it.
Scalable and Flexible Architecture
Log volumes grow as infrastructure grows — and they grow faster than most teams anticipate. A unified platform must scale horizontally without performance degradation, whether you're processing thousands of events per second or millions.
Motadata supports both centralized and distributed deployment models:
Centralized — aggregate all logs into a single repository for organizations that prioritize unified visibility
Distributed — deploy collection nodes across locations with centralized analysis for geographically dispersed environments
The architecture scales with your organization, from initial deployment through enterprise-wide rollout.
Real-Time Log Processing and Alerting
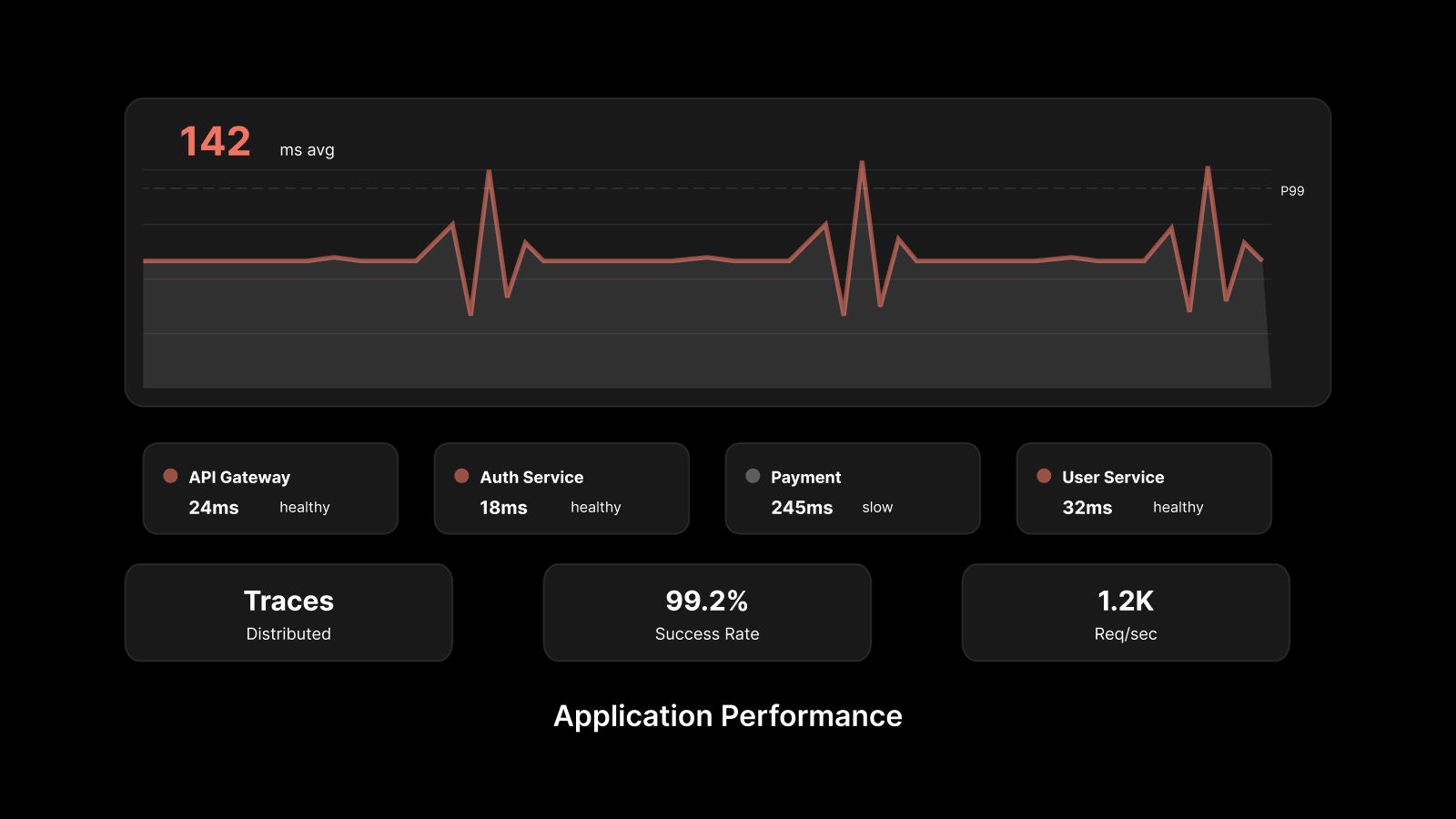
In IT operations, the speed of information is the speed of response. A log event that takes minutes to surface is a log event that causes minutes of unnecessary impact. Unified log analytics must process, index, and surface relevant events in real time.
Motadata's platform delivers sub-second log ingestion and indexing, with real-time dashboards that display events as they happen. Alert rules trigger immediately when conditions are met, and AI-driven anomaly detection identifies deviations from baseline behavior without requiring predefined thresholds.
Security Analytics and Threat Detection
Logs are the primary evidence trail for security investigations. Unified log analytics transforms this evidence from scattered fragments into a coherent narrative:
Correlation across sources — link authentication failures, network traffic anomalies, and application errors to identify attack patterns
Anomaly detection — ML-driven analysis identifies unusual behavior that signature-based detection misses
Forensic investigation — search across all log data with sub-second query response for incident response and threat hunting
Automated remediation suggestions — the platform surfaces relevant actions and remedies when threats are detected
Compliance Reporting and Audit Readiness
Regulatory frameworks — PCI DSS, HIPAA, SOX, FISMA, GDPR, and others — require organizations to collect, retain, and report on log data. Manually assembling compliance evidence from scattered log sources is tedious, error-prone, and fails under audit scrutiny.
A unified platform automates compliance reporting by:
Collecting log data that satisfies framework-specific requirements automatically
Retaining raw data for the duration mandated by each regulation
Generating audit-ready reports with pre-built templates for major compliance standards
Providing tamper-evident log storage that satisfies chain-of-custody requirements
Log Correlation and Root-Cause Analysis
Individual logs tell you that something happened. Correlated logs tell you why. Log correlation triangulates events across infrastructure layers — network, server, application, and security — to identify the causal chain behind incidents.
This is the capability that separates unified log analytics from simple log aggregation. By correlating log events with network flow data, performance metrics, and topology information, the platform pinpoints root causes that no single log stream could reveal in isolation.
Motadata's correlation engine is purpose-built for this cross-layer analysis, enabling teams to move from symptom detection to root-cause identification in minutes rather than hours.
Deployment Options: Agent-Based and Agentless
Unified log analytics platforms must adapt to your environment — not the other way around. Motadata supports multiple collection methods:
Syslog forwarding — standard protocol for network devices and Linux/Unix systems
HTTP/API ingestion — for cloud services and custom applications
Lightweight agents — for endpoints and servers that require local log collection and forwarding
Agentless collection — for environments where installing agents isn't feasible or permitted
This flexibility ensures every log source is captured regardless of the infrastructure's age, architecture, or access constraints.
People Also Ask
What's the difference between log management and log analytics?
Log management focuses on collecting, storing, and retaining logs. Log analytics goes further — it applies search, correlation, pattern detection, and machine learning to extract actionable insights from log data. Unified log analytics combines both into a single platform.
How much log data should an organization retain?
Retention periods depend on regulatory requirements and operational needs. PCI DSS requires one year of log retention with three months immediately accessible. HIPAA requires six years. For operational purposes, 90 days of searchable data with longer-term cold storage is a common baseline.
Can unified log analytics replace a SIEM?
For many organizations, yes. A unified log analytics platform with security correlation, anomaly detection, and compliance reporting capabilities covers the core SIEM use case. However, organizations with advanced threat hunting and incident response requirements may use both in tandem.
How does AI improve log analytics?
AI-driven log analytics applies machine learning to establish behavioral baselines, detect anomalies that static rules miss, correlate events across massive data volumes, and predict issues before they impact users. It transforms logs from a reactive diagnostic tool into a proactive intelligence system.
Conclusion
Unified log analytics isn't a luxury for large enterprises — it's a foundational capability for any organization that depends on IT infrastructure. By consolidating logs from every source into a single platform with real-time processing, AI-driven correlation, and automated compliance reporting, IT teams gain the visibility they need to resolve issues faster, detect threats earlier, and prove compliance without manual effort.
The alternative — scattered log tools, manual correlation, and reactive diagnostics — doesn't scale, doesn't secure, and doesn't satisfy auditors.
Frequently Asked Questions
What is unified log analytics and why is it important?
Unified log analytics centralizes log collection, normalization, and analysis from all IT sources into a single platform. It's important because siloed log management creates blind spots that slow incident resolution, weaken security posture, and complicate compliance reporting.
What log formats does a unified platform support?
A capable unified platform supports all standard log formats — syslog, JSON, CSV, Windows Event Log, cloud-native formats — plus custom and proprietary formats. The platform normalizes incoming data automatically, eliminating the need for custom parsers.
How does log correlation help with incident response?
Log correlation links events across infrastructure layers to reveal the causal chain behind incidents. Instead of investigating symptoms in isolation, teams can trace the root cause across network, server, application, and security logs in a single correlated view.
What compliance standards require centralized log management?
PCI DSS, HIPAA, SOX, FISMA, and GDPR all include requirements for log collection, retention, and reporting. A unified log analytics platform automates compliance by collecting required data, retaining it for mandated periods, and generating audit-ready reports.
How does Motadata approach unified log analytics?
Motadata's AI-native platform ingests logs from any source in any format, normalizes and indexes them in real time, and applies machine learning for anomaly detection and correlation. It supports both agent-based and agentless deployment, scales with your infrastructure, and includes pre-built compliance reporting templates.
Motadata's AI-native log analytics platform delivers unified visibility across your entire IT environment — from network devices and servers to applications and cloud services. Explore Motadata or contact us for a demo to see how centralized log analytics transforms your operations.
Author
Arpit Sharma
Senior Content Marketer
Arpit Sharma is a Senior Content Marketer at Motadata with over 8 years of experience in content writing. Specializing in telecom, fintech, AIOps, and ServiceOps, Arpit crafts insightful and engaging content that resonates with industry professionals. Beyond his professional expertise, he is an avid reader, enjoys running, and loves exploring new places.